
Best Practices when Deploying an Active Directory
Setting up a perfect Active Directory (AD) that will stand the test of time is not as easy as it sounds. Not only do you have to think about the current state of the organization but you also need to plan for future changes. To help you get started I'll be going through the basics about setting up an Active Directory.
What is Active Directory - Server Academy
Establish a plan and stick to it
Take time to map out the current and future state of your IT-environment. Understand how many users, machines, departments and their unique needs exist. Planning now avoids major headaches later.
Keep it simple
The Active Directory is flexible with many components - but complexity often causes issues. Keep the structure and configuration as simple as possible to ensure clarity and maintainability.
Hardware set up
The core of AD is the domain controllers, which validate users. You need redundancy for uptime.
Memory Space
You don’t always need twice the DB size in RAM - just enough to cache the most used data. Proper RAM reduces reliance on disk access and improves authentication speed.
Ensure AD data, log and OS files are on separate physical volumes to avoid performance bottlenecks.
Management plan
Before startup, define responsibilities:
- Who manages AD?
- Is it a team or an individual?
- Are duties divided by OU or domain?
A governance plan helps prevent chaos.
Naming conventions
Standardize object names to simplify troubleshooting.
Users
Common: tjohnsson, tom.johnsson, or tom.b.johnsson.
Avoid using numbers or department names.
Groups
Template: Department + Resource + Group Type + Permissions
Example: Helpdesk-PasswordReset-G
Devices
Format: Type + Location + Asset#
Example: L-HR-1235
Where L = Laptop, HR = Human Resources.
More Architecture Tips
- Separate users and computers into different OUs.
- Create dedicated OUs for security groups and servers.
- Always add descriptions (but never passwords!).
Summary
Want insights into your current AD structure? Use vScope’s Active Directory Documentation and Optimization & Security packs.
👉 Explore Directory Module 👉 vScope Asset Discovery
Recommended reading
Additional sources
Related blog posts
All posts
Webinar Recap: How to Work with Modern IT Governance in vScope
We recently hosted a webinar on modern IT governance with vScope Governance. Here are the key takeaways: on why IT environments become complex, how a governance model works in practice, and how your teams can move from scattered spreadsheets to a living asset register.
From Intune to vScope: Why Endpoint Management Alone Is Not Enough
Intune gives you strong endpoint control. vScope turns that data into shared operational context for operations, security, compliance, and finance.

Why IT inventory initiatives often fail
IT inventory and discovery promise control, security, and cost clarity—yet many projects stall. Here's why they falter without the right platform, and what reliable discovery should look like.

Microsoft 365 Pricing Changes 2026: What It Means for Your Budget
Microsoft is updating pricing and packaging for Microsoft 365 in 2026. Here’s what the currency adjustments and July price increases mean – and how CIOs and M365 admins should respond.

Effective Configuration Management Requires Transparency Across All Systems
In modern IT environments, the gap between reported and actual configuration is bigger than most people realize. In this article, I explain why accurate inventory requires collecting data about each asset from multiple sources – not just one.
How Lifecycle Cost Analysis Helps You Make Smarter IT Decisions
IT teams are under constant pressure to deliver more with less. But without understanding the true cost of every server, license, or laptop, even the most well-planned budgets can spiral out of control.

How Microsoft's New Licensing Model Impacts You - and How to Prepare with vScope
Starting November 2025, Microsoft will remove volume discounts in Enterprise Agreement, MPSA, and OSPA. In this article, we explain what the change means for your organization, and how vScope helps you gain full visibility and control of licenses and costs across your environment.
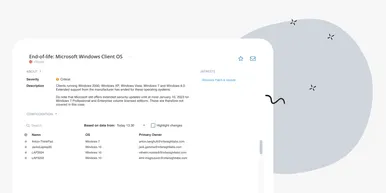
Last Day for Windows 10 - Are Your Clients Ready?
As of October 15, 2025, Microsoft officially ends support for Windows 10. In this article, we explore what that means, why Microsoft is making this change, and how you can use vScope’s inventory and prebuilt insights to stay ahead.
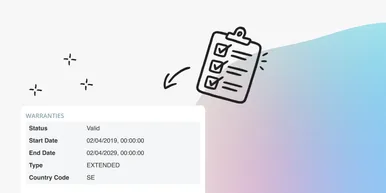
Warranty Management in Practice: Checklist, Pitfalls, and How to Automate with vScope
Learn how to manage device warranties the right way. We walk through a step-by-step checklist for manual warranty tracking and how to automate follow-ups, reports, and alerts with vScope Discovery.